Create Copy Image of USB Drive
The first thing we will do is make a copy of the USB drive. In this case, regular backups will not work. This is a very crucial step, and if it is done wrong, all the work will go to waste. Use the following command to list all the drives attached to the system:
In Linux, the drive names are different from Windows. In a Linux system, hda and hdb are used (sda, sdb, sdc, etc.) for SCSI, unlike in Windows OS.
Now that we have the drive name, we can create its .dd image bit-by-bit with the dd utility by entering the following command:
if=the location of the USB drive
of=the destination where the copied image will be stored (can be a local path on your system, e.g. /home/user/usb.dd)
bs=the number of bytes that will be copied at a time
To secure proof that we have the original image copy of the drive, we will use hashing to maintain the image’s integrity. Hashing will provide a hash for the USB drive. If a single bit of data is changed, the hash will be changed completely, and one will know if the copy is fake or original. We will generate an md5 hash of the drive so that, when compared with the drive’s original hash, no one can question the integrity of the copy.
This will provide an md5 hash of the image. Now, we can start our forensics analysis on this newly created image of the USB drive, along with the hash.
Boot Sector Layout
Running the file command will give back the file system, as well as the drive’s geometry:
ok.dd: DOS/MBR boot sector, code offset 0x58+2, OEM-ID "MSDOS5.0",
sectors/cluster 8, reserved sectors 4392, Media descriptor 0xf8,
sectors/track 63, heads 255, hidden sectors 32, sectors 1953760 (volumes > 32 MB),
FAT (32 bit), sectors/FAT 1900, reserved 0x1, serial number 0x6efa4158, unlabeled
Now, we can use the minfo tool to get the NTFS boot sector layout and the boot sector information via the following command:
device information:
===================
filename="ok.dd"
sectors per track: 63
heads: 255
cylinders: 122
mformat command line: mformat -T 1953760 -i ok.dd -h 255 -s 63 -H 32 ::
boot sector information
======================
banner:"MSDOS5.0"
sector size: 512 bytes
cluster size: 8 sectors
reserved (boot) sectors: 4392
fats: 2
max available root directory slots: 0
small size: 0 sectors
media descriptor byte: 0xf8
sectors per fat: 0
sectors per track: 63
heads: 255
hidden sectors: 32
big size: 1953760 sectors
physical drive id: 0x80
reserved=0x1
dos4=0x29
serial number: 6EFA4158
disk label="NO NAME "
disk type="FAT32 "
Big fatlen=1900
Extended flags=0x0000
FS version=0x0000
rootCluster=2
infoSector location=1
backup boot sector=6
Infosector:
signature=0x41615252
free clusters=243159
last allocated cluster=15
Another command, the fstat command, can be used to obtain general known info, such as allocation structures, layout, and boot blocks, about the device image. We will use the following command to do so:
--------------------------------------------
File System Type: FAT32
OEM Name: MSDOS5.0
Volume ID: 0x6efa4158
Volume Label (Boot Sector): NO NAME
Volume Label (Root Directory): KINGSTON
File System Type Label: FAT32
Next Free Sector (FS Info): 8296
Free Sector Count (FS Info): 1945272
Sectors before file system: 32
File System Layout (in sectors)
Total Range: 0 - 1953759
* Reserved: 0 - 4391
** Boot Sector: 0
** FS Info Sector: 1
** Backup Boot Sector: 6
* FAT 0: 4392 - 6291
* FAT 1: 6292 - 8191
* Data Area: 8192 - 1953759
** Cluster Area: 8192 - 1953759
*** Root Directory: 8192 - 8199
METADATA INFORMATION
--------------------------------------------
Range: 2 - 31129094
Root Directory: 2
CONTENT INFORMATION
--------------------------------------------
Sector Size: 512
Cluster Size: 4096
Total Cluster Range: 2 - 243197
FAT CONTENTS (in sectors)
--------------------------------------------
8192-8199 (8) -> EOF
8200-8207 (8) -> EOF
8208-8215 (8) -> EOF
8216-8223 (8) -> EOF
8224-8295 (72) -> EOF
8392-8471 (80) -> EOF
8584-8695 (112) -> EOF
Deleted Files
The Sleuth Kit provides the fls tool, which provides all the files (especially recently deleted files) in each path, or in the image file specified. Any information about deleted files can be found using the fls utility. Enter the following command to use the fls tool:
r/r 3: KINGSTON (Volume Label Entry)
d/d 6: System Volume Information
r/r 135: System Volume Information/WPSettings.dat
r/r 138: System Volume Information/IndexerVolumeGuid
r/r * 14: Game of Thrones 1 720p x264 DDP 5.1 ESub - xRG.mkv
r/r * 22: Game of Thrones 2 (Pretcakalp) 720 x264 DDP 5.1 ESub - xRG.mkv
r/r * 30: Game of Thrones 3 720p x264 DDP 5.1 ESub - xRG.mkv
r/r * 38: Game of Thrones 4 720p x264 DDP 5.1 ESub - xRG.mkv
d/d * 41: Oceans Twelve (2004)
r/r 45: MINUTES OF PC-I HELD ON 23.01.2020.docx
r/r * 49: MINUTES OF LEC HELD ON 10.02.2020.docx
r/r * 50: windump.exe
r/r * 51: _WRL0024.tmp
r/r 55: MINUTES OF LEC HELD ON 10.02.2020.docx
d/d * 57: New folder
d/d * 63: tender notice for network infrastructure equipment
r/r * 67: TENDER NOTICE (Mega PC-I) Phase-II.docx
r/r * 68: _WRD2343.tmp
r/r * 69: _WRL2519.tmp
r/r 73: TENDER NOTICE (Mega PC-I) Phase-II.docx
v/v 31129091: $MBR
v/v 31129092: $FAT1
v/v 31129093: $FAT2
d/d 31129094: $OrphanFiles
-/r * 22930439: $bad_content1
-/r * 22930444: $bad_content2
-/r * 22930449: $bad_content3
Here, we have obtained all the relevant files. The following operators were used with the fls command :
-p =used to display the full path of every file recovered
-r =used to display the paths and folders recursively
-f =the type of file system used (FAT16, FAT32, etc.)
The above output shows that the USB drive contains many files. The deleted files recovered are notated with a “*” sign. You can see that something is not normal with the files named $bad_content1, $bad_content2, $bad_content3, and windump.exe. Windump is a network traffic capture tool. Using the windump tool, one can capture data not meant for the same computer. The intent is shown in the fact that the software windump has the specific purpose to capture network traffic and was intentionally used to gain access to the personal communications of a legitimate user.
Timeline Analysis
Now that we have an image of the file system, we can perform MAC timeline analysis of the image to generate a timeline and to place the contents with the date and time in a systematic, readable format. Both the fls and ils commands can be used to build a timeline analysis of the file system. For the fls command, we need to specify that the output will be in MAC timeline output format. To do so, we will run the fls command with the -m flag and redirect the output to a file. We will also use the -m flag with the ils command.
[email protected]:~$ cat usb.fls
0|/KINGSTON (Volume Label Entry)|3|r/rrwxrwxrwx|0|0|0|0|1531155908|0|0
0|/System Volume Information|6|d/dr-xr-xr-x|0|0|4096|1531076400|1531155908|0|1531155906
0|/System Volume Information/WPSettings.dat|135|r/rrwxrwxrwx|0|0|12|1532631600|1531155908|0|1531155906
0|/System Volume Information/IndexerVolumeGuid|138|r/rrwxrwxrwx|0|0|76|1532631600|1531155912|0|1531155910
0|Game of Thrones 1 720p x264 DDP 5.1 ESub - xRG.mkv (deleted)|14|r/rrwxrwxrwx|0|0|535843834|1531076400|1531146786|0|1531155918
0|Game of Thrones 2 720p x264 DDP 5.1 ESub - xRG.mkv(deleted)|22|r/rrwxrwxrwx|0|0|567281299|1531162800|1531146748|0|1531121599
0|/Game of Thrones 3 720p x264 DDP 5.1 ESub - xRG.mkv(deleted)|30|r/rrwxrwxrwx|0|0|513428496|1531162800|1531146448|0|1531121607
0|/Game of Thrones 4 720p x264 DDP 5.1 ESub - xRG.mkv(deleted)|38|r/rrwxrwxrwx|0|0|567055193|1531162800|1531146792|0|1531121680
0|/Oceans Twelve (2004) (deleted)|41|d/drwxrwxrwx|0|0|0|1532545200|1532627822|0|1532626832
0|/MINUTES OF PC-I HELD ON 23.01.2020.docx|45|r/rrwxrwxrwx|0|0|33180|1580410800|1580455238|0|1580455263
0|/MINUTES OF LEC HELD ON 10.02.2020.docx (deleted)|49|r/rrwxrwxrwx|0|0|46659|1581966000|1581932204|0|1582004632
0|/_WRD3886.tmp (deleted)|50|r/rrwxrwxrwx|0|0|38208|1581966000|1582006396|0|1582004632
0|/_WRL0024.tmp (deleted)|51|r/rr-xr-xr-x|0|0|46659|1581966000|1581932204|0|1582004632
0|/MINUTES OF LEC HELD ON 10.02.2020.docx|55|r/rrwxrwxrwx|0|0|38208|1581966000|1582006396|0|1582004632
(deleted)|67|r/rrwxrwxrwx|0|0|56775|1589482800|1589528598|0|1589528701
0|/_WRD2343.tmp (deleted)|68|r/rrwxrwxrwx|0|0|56783|1589482800|1589528736|0|1589528701
0|/_WRL2519.tmp (deleted)|69|r/rr-xr-xr-x|0|0|56775|1589482800|1589528598|0|1589528701
0|/TENDER NOTICE (Mega PC-I) Phase-II.docx|73|r/rrwxrwxrwx|0|0|56783|1589482800|1589528736|0|1589528701
0|/$MBR|31129091|v/v---------|0|0|512|0|0|0|0
0|/$FAT1|31129092|v/v---------|0|0|972800|0|0|0|0
0|/$FAT2|31129093|v/v---------|0|0|972800|0|0|0|0
0|/New folder (deleted)|57|d/drwxrwxrwx|0|0|4096|1589482800|1589528384|0|1589528382
0|Windump.exe (deleted)|63|d/drwxrwxrwx|0|0|4096|1589482800|1589528384|0|1589528382
0|/TENDER NOTICE (Mega PC-I) Phase-II.docx (deleted)|67|r/rrwxrwxrwx|0|0|56775|1589482800|1589528598|0|1589528701
0|/_WRD2343.tmp (deleted)|68|r/rrwxrwxrwx|0|0|56783|1589482800|1589528736|0|1589528701
0|/_WRL2519.tmp (deleted)|69|r/rr-xr-xr-x|0|0|56775|1589482800|1589528598|0|1589528701
0|/TENDER NOTICE (Mega PC-I) Phase-II.docx|73|r/rrwxrwxrwx|0|0|56783|1589482800|1589528736|0|1589528701
0|/$MBR|31129091|v/v---------|0|0|512|0|0|0|0
0|/$FAT1|31129092|v/v---------|0|0|972800|0|0|0|0
0|/$FAT2|31129093|v/v---------|0|0|972800|0|0|0|0
0|/$OrphanFiles|31129094|d/d---------|0|0|0|0|0|0|0
0|/$$bad_content 1 (deleted)|22930439|-/rrwxrwxrwx|0|0|59|1532631600|1532627846|0|1532627821
0|/$$bad_content 2 (deleted)|22930444|-/rrwxrwxrwx|0|0|47|1532631600|1532627846|0|1532627821
0|/$$bad_content 3 (deleted)|22930449|-/rrwxrwxrwx|0|0|353|1532631600|1532627846|0|1532627821
Run the mactime tool to obtain timeline analysis with the following command:
To convert this mactime output to human-readable form, enter the following command:
Thu Jul 26 2018 22:57:26 59 m... -/rrwxrwxrwx 0 0 22930439 /Game of Thrones 4 720p x264 DDP 5.1 ESub -(deleted)
47 m... -/rrwxrwxrwx 0 0 22930444 /Game of Thrones 4 720p x264 DDP 5.1 ESub - (deleted)
353 m... -/rrwxrwxrwx 0 0 22930449 //Game of Thrones 4 720p x264 DDP 5.1 ESub - (deleted)
Fri Jul 27 2018 00:00:00 12 .a.. r/rrwxrwxrwx 0 0 135 /System Volume Information/WPSettings.dat
76 .a.. r/rrwxrwxrwx 0 0 138 /System Volume Information/IndexerVolumeGuid
59 .a.. -/rrwxrwxrwx 0 0 22930439 /Game of Thrones 3 720p x264 DDP 5.1 ESub 3(deleted)
47 .a.. -/rrwxrwxrwx 0 0 22930444 $/Game of Thrones 3 720p x264 DDP 5.1 ESub 3 (deleted)
353 .a.. -/rrwxrwxrwx 0 0 22930449 /Game of Thrones 3 720p x264 DDP 5.1 ESub 3 (deleted)
Fri Jan 31 2020 00:00:00 33180 .a.. r/rrwxrwxrwx 0 0 45 /MINUTES OF PC-I HELD ON 23.01.2020.docx
Fri Jan 31 2020 12:20:38 33180 m... r/rrwxrwxrwx 0 0 45 /MINUTES OF PC-I HELD ON 23.01.2020.docx
Fri Jan 31 2020 12:21:03 33180 ...b r/rrwxrwxrwx 0 0 45 /MINUTES OF PC-I HELD ON 23.01.2020.docx
Mon Feb 17 2020 14:36:44 46659 m... r/rrwxrwxrwx 0 0 49 /MINUTES OF LEC HELD ON 10.02.2020.docx (deleted)
46659 m... r/rr-xr-xr-x 0 0 51 /_WRL0024.tmp (deleted)
Tue Feb 18 2020 00:00:00 46659 .a.. r/rrwxrwxrwx 0 0 49 /Game of Thrones 2 720p x264 DDP 5.1 ESub -(deleted)
38208 .a.. r/rrwxrwxrwx 0 0 50 /_WRD3886.tmp (deleted)
Tue Feb 18 2020 10:43:52 46659 ...b r/rrwxrwxrwx 0 0 49 /Game of Thrones 1 720p x264 DDP 5.1 ESub -
38208 ...b r/rrwxrwxrwx 0 0 50 /_WRD3886.tmp (deleted)
46659 ...b r/rr-xr-xr-x 0 0 51 /_WRL0024.tmp (deleted)
38208 ...b r/rrwxrwxrwx 0 0 55 /MINUTES OF LEC HELD ON 10.02.2020.docx
Tue Feb 18 2020 11:13:16 38208 m... r/rrwxrwxrwx 0 0 50 /_WRD3886.tmp (deleted)
46659 .a.. r/rr-xr-xr-x 0 0 51 /_WRL0024.tmp (deleted)
38208 .a.. r/rrwxrwxrwx 0 0 55 /MINUTES OF LEC HELD ON 10.02.2020.docx
Tue Feb 18 2020 10:43:52 46659 ...b r/rrwxrwxrwx 0 0 49 /Game of Thrones 1 720p x264 DDP 5.1 ESub -
38208 ...b r/rrwxrwxrwx 0 0 50 /_WRD3886.tmp (deleted)
46659 ...b r/rr-xr-xr-x 0 0 51 /_WRL0024.tmp (deleted)
38208 ...b r/rrwxrwxrwx 0 0 55 /MINUTES OF LEC HELD ON 10.02.2020.docx
Tue Feb 18 2020 11:13:16 38208 m... r/rrwxrwxrwx 0 0 50 /_WRD3886.tmp (deleted)
38208 m... r/rrwxrwxrwx 0 0 55 /Game of Thrones 3 720p x264 DDP 5.1 ESub -
Fri May 15 2020 00:00:00 4096 .a.. d/drwxrwxrwx 0 0 57 /New folder (deleted)
4096 .a.. d/drwxrwxrwx 0 0 63 /tender notice for network infrastructure equipment for IIUI (deleted)
56775 .a.. r/rrwxrwxrwx 0 0 67 /TENDER NOTICE (Mega PC-I) Phase-II.docx (deleted)
56783 .a.. r/rrwxrwxrwx 0 0 68 /_WRD2343.tmp (deleted)
56775 .a.. r/rr-xr-xr-x 0 0 69 /_WRL2519.tmp (deleted)
56783 .a.. r/rrwxrwxrwx 0 0 73 /TENDER NOTICE (Mega PC-I) Phase-II.docx
Fri May 15 2020 12:39:42 4096 ...b d/drwxrwxrwx 0 0 57 /New folder (deleted)
4096 ...b d/drwxrwxrwx 0 0 63 /tender notice for network infrastructure equipment for IIUI (deleted)
Fri May 15 2020 12:39:44 4096 m... d/drwxrwxrwx 0 0 57 $$bad_content 3(deleted)
4096 m... d/drwxrwxrwx 0 0 63 /tender notice for network infrastructure equipment for IIUI (deleted)
Fri May 15 2020 12:43:18 56775 m... r/rrwxrwxrwx 0 0 67$$bad_content 1 (deleted)
56775 m... r/rr-xr-xr-x 0 0 69 /_WRL2519.tmp (deleted)
Fri May 15 2020 12:45:01 56775 ...b r/rrwxrwxrwx 0 0 67 $$bad_content 2 (deleted)
56783 ...b r/rrwxrwxrwx 0 0 68 /_WRD2343.tmp (deleted)
56775 ...b r/rr-xr-xr-x 0 0 69 /_WRL2519.tmp (deleted)
56783 ...b r/rrwxrwxrwx 0 0 73 /TENDER NOTICE (Mega PC-I) Phase-II.docx
Fri May 15 2020 12:45:36 56783 m... r/rrwxrwxrwx 0 0 68 windump.exe (deleted)
56783 m... r/rrwxrwxrwx 0 0 73 /TENDER NOTICE (Mega PC-I) Phase-II.docx
All the files should be recovered with a timestamp on it in a human-readable format in the file “usb.mactime.”
Tools for USB Forensics Analysis
There are various tools that can be used to perform forensics analysis on a USB drive, such as Sleuth Kit Autopsy, FTK Imager, Foremost, etc. First, we will have a look at the Autopsy tool.
Autopsy
Autopsy is used to extract and analyze data from different types of images, such as AFF (Advance Forensic Format) images, .dd images, raw images, etc. This program is a powerful tool used by forensic investigators and different law enforcement agencies. Autopsy consists of many tools that can help investigators to get the job done efficiently and smoothly. The Autopsy tool is available for both Windows and UNIX platforms free of cost.
To analyze a USB image using Autopsy, you must first create a case, including writing the investigators’ names, recording the case name, and other informational tasks. The next step is to import the source image of the USB drive obtained at the start of the process using the dd utility. Then, we will let the Autopsy tool do what it does best.
The amount of information provided by Autopsy is enormous. Autopsy provides the original filenames and also allows you to examine the directories and paths with all the info about the relevant files, such as accessed, modified, changed, date, and time. The metadata info is also retrieved, and all the info is sorted in a professional way. To make the file search easier, Autopsy provides a Keyword Search option, which allows the user to quickly and efficiently search a string or number from among the retrieved contents.
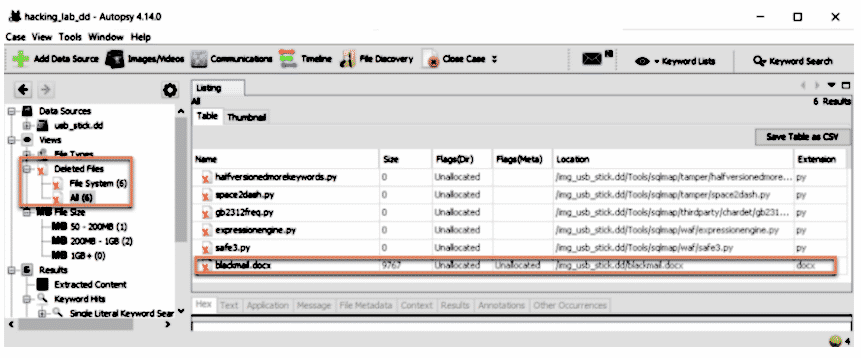
In the left panel of the subcategory of File Types, you will see a category named “Deleted Files” containing the deleted files from the desired drive image with all the Metadata and Timeline Analysis information.
Autopsy is Graphic User Interface (GUI) for the command-line tool Sleuth Kit and is at the top level in the forensics world due to its integrity, versatility, easy-to-use nature, and the ability to produce fast results. USB device forensics can be performed as easily on Autopsy as on any other paid tool.
FTK Imager
FTK Imager is another great tool used for the retrieval and acquisition of data from different types of images provided. FTK Imager also has the ability to make a bit-by-bit image copy, so that no other tool like dd or dcfldd is needed for this purpose. This copy of the drive includes all files and folders, the unallocated and free space, and the deleted files left in slack space or unallocated space. The basic goal here when performing forensic analysis on USB drives is to reconstruct or recreate the attack scenario.
We will now take a look at performing USB forensics analysis on a USB image using the FTK Imager tool.
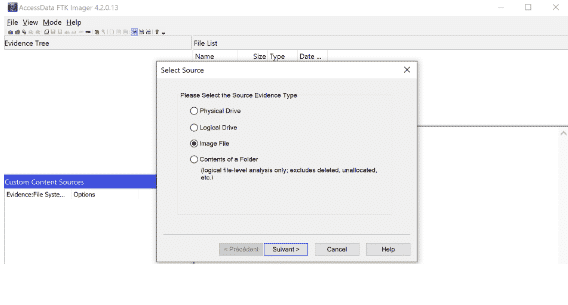
First, add the image file to FTK Imager by clicking File >> Add Evidence Item.
Now, select the type of file you want to import. In this case, it is an image file of a USB drive.
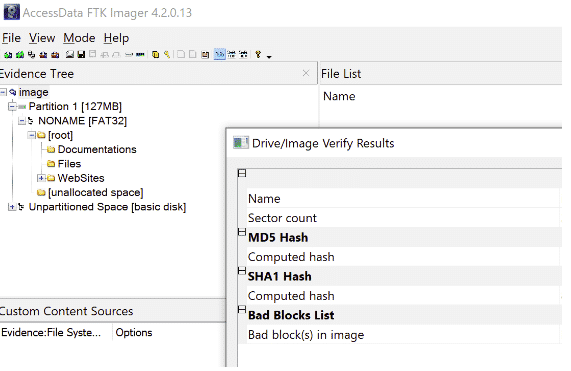
Now, enter the full location of the image file. Remember, you must provide a full path for this step. Click Finish to begin data acquisition, and let the FTK Imager do the job. After some time, the tool will provide the desired results.
Here, the first thing to do is to verify Image Integrity by right-clicking on the image name and selecting Verify Image. The tool will check for matching md5 or SHA1 hashes provided with the image information, and will also tell you whether the image has been tampered with before being imported into the FTK Imager tool.
Now, Export the given results to the path of your choice by right-clicking the image name and selecting the Export option to analyze it. The FTK Imager will create a full data log of the forensics process and will place these logs in the same folder as the image file.
Analysis
The recovered data can be in any format, such as tar, zip (for compressed files), png, jpeg, jpg (for image files), mp4, avi format (for video files), barcodes, pdfs, and other file formats. You should analyze the metadata of the given files and check for barcodes in the form of a QR Code. This can be in a png file and can be retrieved using the ZBAR tool. In most cases, docx and pdf files are used to hide statistical data, so they must be uncompressed. Kdbx files can be opened through Keepass; the password may have been stored in other recovered files, or we can perform bruteforce at any time.
Foremost
Foremost is a tool used to recover deleted files and folders from a drive image using headers and footers. We will take a look at Foremost’s man page to explore some powerful commands contained within this tool:
-a Enables write all headers, perform no error detection in terms
of corrupted files.
-b number
Allows you to specify the block size used in foremost. This is
relevant for file naming and quick searches. The default is
512. ie. foremost -b 1024 image.dd
-q (quick mode) :
Enables quick mode. In quick mode, only the start of each sector
is searched for matching headers. That is, the header is
searched only up to the length of the longest header. The rest
of the sector, usually about 500 bytes, is ignored. This mode
makes foremost run considerably faster, but it may cause you to
miss files that are embedded in other files. For example, using
quick mode you will not be able to find JPEG images embedded in
Microsoft Word documents.
Quick mode should not be used when examining NTFS file systems.
Because NTFS will store small files inside the Master File Ta‐
ble, these files will be missed during quick mode.
-a Enables write all headers, perform no error detection in terms
of corrupted files.
-i (input) file :
The file used with the i option is used as the input file.
In the case that no input file is specified stdin is used to c.
The file used with the i option is used as the input file.
In the case that no input file is specified stdin is used to c.
To get the job done, we will use the following command :
After the process is complete, there will be a file in the /output folder named text containing the results.
Conclusion
USB drive forensics is a good skill to have to retrieve evidence and recover deleted files from a USB device, as well as to identify and examine what computer programs may have been used in the attack. Then, you may put together the steps the attacker may have taken to prove or disprove the claims made by the legitimate user or victim. To ensure that no one gets away with a cyber-crime involving USB data, USB forensics is an essential tool. USB devices contain key evidence in most forensics cases and sometimes, the forensics data obtained from a USB drive can help in recovering important and valuable personal data.